Protect Exchange OWA from Brute-Force attack
Security has been major concern these days… and email is one of the most. There are several vulnerabilities in the email services and we are going to talk about the OWA. On this blog we will be discussing on how we can Protect Exchange OWA from Brute-Force attack.
As we know the back-bone authentication for the Exchange OWA is Active Directory. and through the Active Directory, we can secure the authentication. Even though user is lockout in Active Directory, they can still access on their email. i.e. User is authentication on the OWA. Which shows us on the vulnerabilities Brute-Force attack on Exchange OWA login. Anyone can simultaneously enter random password without getting lockout. Hence the question arises, how can we protect our OWA.
Resolution:
Step1: Maintain Password Policy from Active Directory Domain Controller
To protect the OWA from Brute-Force attack we can proceed with simple things. First, we need to manage the password policy on our Active Directory.
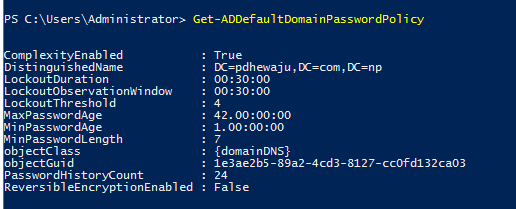
To get manage this policy, we can simply configure it from the Group Policy. Selecting the password policy GPO.
Step 2: Configure the cache for IIS authentication
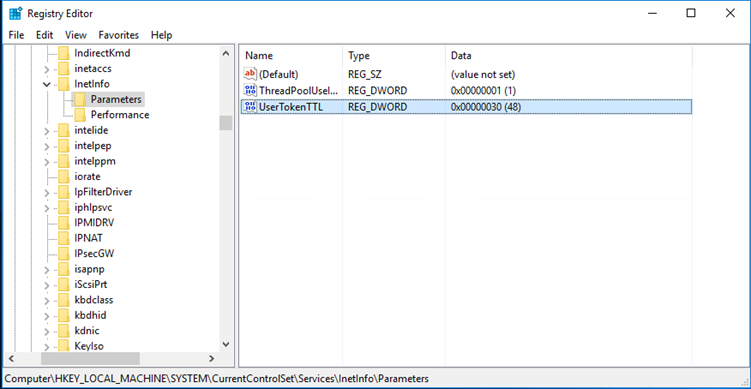
Once the Password Policy has been maintained the next step is to configure the cache for IIS authentication. As I have mentioned earlier, even though user is locked on Active Directory they will still get access on the OWA Portal. So to stop it, we need to reduce the cache of the IIS website. To reduce the cache we need to perform below action.
- Open Regedit on Exchange CAS server.
- Go to HKLM\SYSTEM\CurrentControlSET\Services\InetInfo\Parameters
-
Create a new DWORD with name UserTokenTTL and keep the value 30 ( this means keeping the Cache only for 30 Sec).
Now, if the user enters few number of wrong password. Then user will not be able to login into their OWA or get authenticate until account is unlocked by administrator.
Hope this will help you to protect from the Brute-force attack.

Excellent post my dear friend
This will not help, this is stupid advice, because an attacker can block mail accounts, everyone will wait for the system administrator to unlock the accounts. In this situation, it will be very expensive for the company.
There is several options for protection:
1. Use client certificate to access to OWA
2. Use captcha
Both of these recommendations will reduce bruteforce attack.
Thank you Mike for your insight. I hope we can have some additional function with 3rd party application integration on OWA for two Factor authentication.