Azure AD My Sign-Ins Activity Report
Security has been one of the most concern topic since very long in IT industry, but now it comes with transparency. Everyone wants transparency with the system logs. Looking a part of transparency, Azure AD has been provided by new feature to get report of your sign-ins. It seems to be like normal and reactive feature for the incident but is quite important evidence for the suspicious login in specific account. Like,
- If anyone is trying to guess their password.
- If an attacker successfully signed into their account from a strange location. (in other words, somewhere that the user knows they weren’t at the time).
- What apps the attacker accessed.
And the best part, you don’t require to ask your admin to check all these activities. It’s on your own fingertips.
How to access My Sign-Ins
To access My Sign-ins, you can simply click on this link or you can follow below instructions.
Step 1: Get login to your Office 365 Portal.
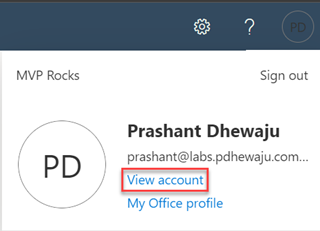
Step 2: Click on your profile and select view profile.
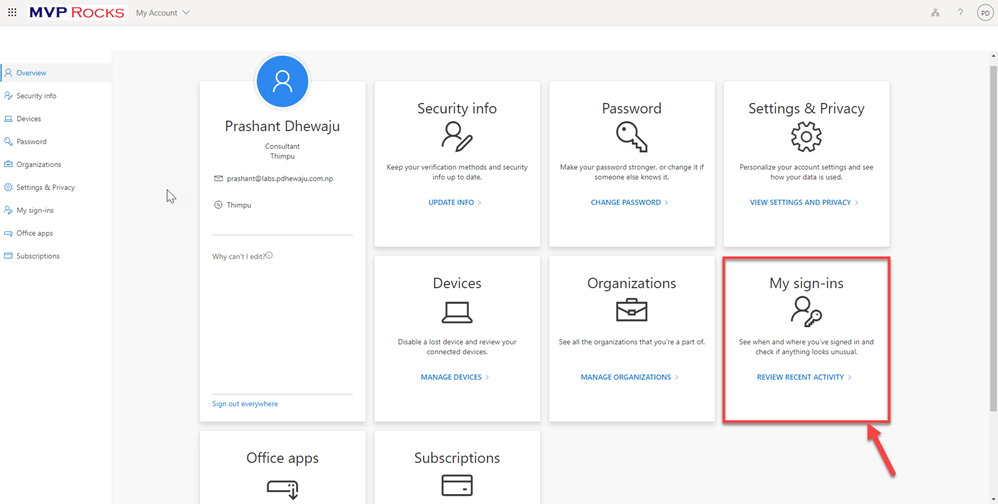
Step 3: On your account settings you will see My Sign-Ins. Click on it to get explore.
Step 4: You will be able to see you login information’s.
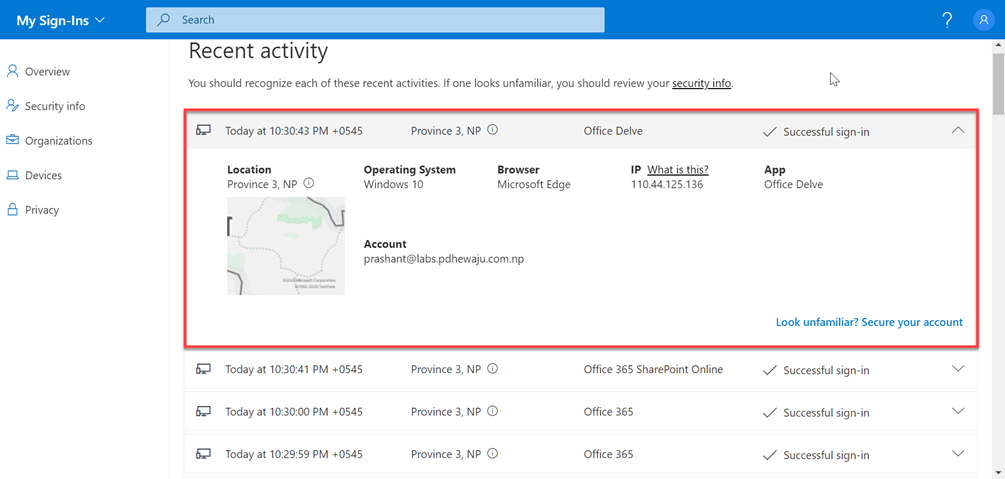
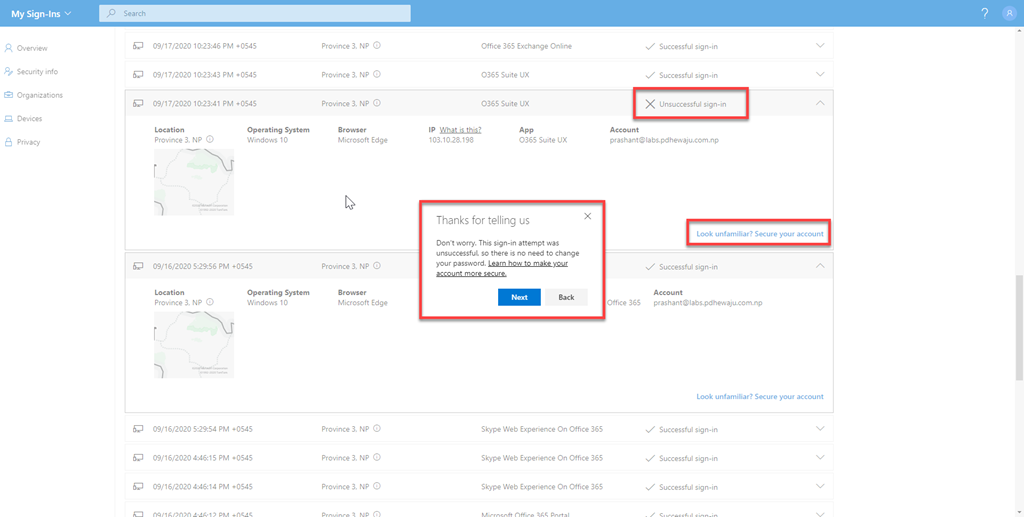
So basically, with this page you will get an information with below details:
- Time with time zone
- Detail Location
- Operating System
- Browser
- Client Public IP Address
- Application (App)
- Account (my own account name)
- Sign-In Status (Successful/unsuccessful).
So, what will happen when there is some thing unsuccessful? Should I need to change my password? Okay, so it’s quite easy now. If you find there has been unsuccessful sign-ins from unknown location, you can click on ‘Look unfamiliar? Secure your account‘.
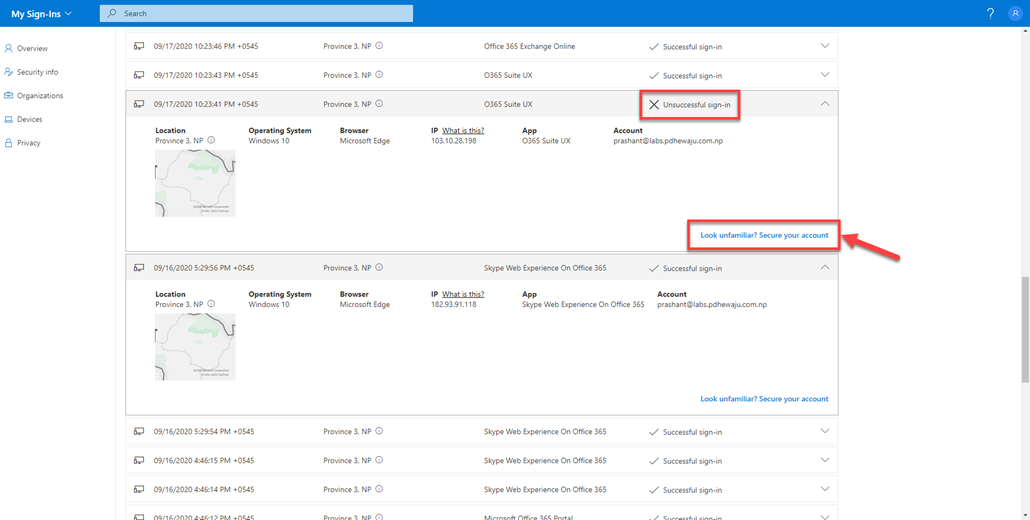
Once you click on that, you will get a suggestion what next need to be done to make your account secure.
I hope this will help you to get transparent with the account of your own in Microsoft 365.
If you’re curious about your personal email too, we have similar features in the Recent Activity page for consumer Microsoft Accounts at: https://account.live.com/activity – Check it out!
![[error]The Single Instance Store (SIS) component is not installed](/wp-content/themes/ribbon-lite/images/nothumb-related.png)

